Part 1, part 2, and part 3 established a clear pattern.
Part 1 (Terraform): strong deployment-time baseline, but runtime drift and child-resource gaps remain.
Part 2 (CloudFormation): strong template-time controls and hooks, but uneven propagation and non-pipeline paths still exist.
Part 3 (disadvantages): IaC + Tag Policies alone cannot deliver full lifecycle governance in dynamic AWS environments.
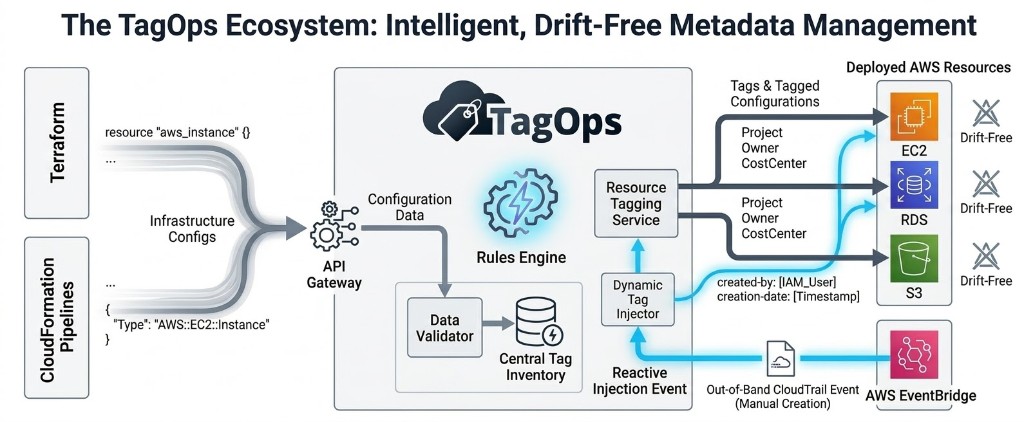
To permanently solve the tag governance gap, tagging logic must be decoupled from static IaC files, rigid SCPs, and restrictive AWS Tag Policies. Tagging logic must be centralized in a dynamic, intelligent engine that integrates seamlessly with both deployment pipelines and out-of-band events. TagOps bridges this gap by providing real-time tag synchronization without causing IaC drift, and without colliding with AWS API quotas.
This final part focuses on execution: how TagOps closes those gaps without replacing Terraform or CloudFormation.
| Layer | Primary job | Owned by |
|---|---|---|
| Terraform / CloudFormation | Deterministic deployment and baseline tags | Platform / infra teams |
| AWS Tag Policies / SCPs | Taxonomy guardrails and hard safety rails | Cloud governance / security |
| TagOps | Continuous runtime enforcement and enrichment | Platform + FinOps, shared |
Why IaC-Only Governance Breaks in Practice
Platform teams usually operate two parallel realities:
- Declared intent: tags in Terraform/CloudFormation code.
- Runtime reality: resources created/modified by AWS services, operators, and external tools.
Governance failures happen where these realities diverge. The fix is not "more static policy." The fix is a runtime-capable governance layer that stays aligned with IaC contracts.
TagOps Design Principle: Baseline + Continuous Control
TagOps treats IaC as the source of deployment intent, then continuously executes tagging policy after deployment.
Core principle:
- keep Terraform/CloudFormation as the baseline delivery engine
- centralize tag contract logic in one policy layer
- Terraform/CloudFormation integration with TagOps
- enforce continuously via TagOps event and scan mechanisms
This removes the false choice between "developer velocity" and "governance correctness."
Mental model
Think of TagOps as a runtime control plane for tags that reads from your IaC intent, not as “another place to define infrastructure.”
Terraform Integration: In-Band Policy-Computed Tags
TagOps reduces Terraform state conflicts using the public
terraform-aws-tagops module. Instead of
hardcoding all tagging logic in HCL across many modules, teams can centralize policy logic in TagOps and consume computed tag outputs during Terraform
workflows.
TagOps calculates final tags by merging three sources in a clear priority order (lowest to highest):
- Default Tags: baseline tags defined at the provider level, passed via the
default_tagsvariable. - Resource Tags: existing, hardcoded tags on specific resources, passed via
custom_resources. - TagOps Rule Tags: tags intelligently calculated by the TagOps rules engine based on your organization's business logic.
Because Terraform receives policy-computed tags and applies them in-band, state alignment improves significantly and drift loops are reduced. This does not mean all drift disappears in every scenario, but it greatly decreases conflict between static IaC definitions and runtime governance actions.
TagOps injects governed tag values at deploy time, so central policy updates can be applied without rewriting tag logic in every Terraform module.
Practical result:
- Terraform applies already-governed values.
- Drift loops are reduced because policy logic is injected in-band.
- Teams avoid scattering complex tag logic across many modules.
Outcome
Platform teams keep Terraform as-is, but get governed tags “for free” from a central engine instead of hand-coding every rule in HCL.
Terraform Example
locals {
default_tags = {
managed-by = "terraform"
environment-name = "production"
}
}
data "aws_ssm_parameter" "tagops_api_token" {
name = "/tagops/api_token"
with_decryption = true
}
module "tagops" {
source = "tagops/tagops/aws"
version = "~> 0.1.1"
api_token = data.aws_ssm_parameter.tagops_api_token.value
default_tags = local.default_tags
default_resources = [
"aws_vpc",
"aws_subnet",
"aws_internet_gateway",
"aws_route_table",
"aws_nat_gateway",
"aws_eip",
"aws_network_acl",
"aws_security_group",
]
}
module "vpc" {
source = "terraform-aws-modules/vpc/aws"
version = "6.5.1"
name = "production"
cidr = "10.0.0.0/16"
# ...
vpc_tags = merge(module.tagops.tags["default_aws_vpc"], { Name = "vpc-production" })
igw_tags = merge(module.tagops.tags["default_aws_internet_gateway"], { Name = "igw-production" })
nat_gateway_tags = merge(module.tagops.tags["default_aws_nat_gateway"], { Name = "nat-production" })
nat_eip_tags = merge(module.tagops.tags["default_aws_eip"], { Name = "eip-production-nat" })
}
In this pattern, each resource-specific tag map is composed with merge(...) so Terraform receives a deterministic final value while policy logic
remains centrally managed.
More information and implementation examples are available in the TagOps Terraform integration documentation.
CloudFormation Integration: Enforce Contract Before and During Deploy
For teams utilizing CloudFormation, TagOps leverages AWS CloudFormation Macros (Transform: TagOps). CloudFormation macros let you run custom
processing on templates before deployment-from simple string replacements to full template transformations. When you declare a macro in the
Transform section of your template and a stack is deployed, the macro intercepts the template and invokes a proxy Lambda function deployed
securely in your account. This Lambda forwards the template fragment to the TagOps SaaS API.
Similar to the Terraform integration, TagOps evaluates the template, merges TagOpsCustomTags (template-level metadata) with resource-level tags
and its own rule-based tags. It seamlessly injects the missing tags directly into the CloudFormation JSON/YAML, returning the fully transformed template to
CloudFormation before the resources are provisioned. Developers no longer need to bloat their templates with complex tagging arrays or worry about failing
strict CloudFormation Hooks.
For more details on how macros work, see the AWS CloudFormation Macros documentation.
For CloudFormation, TagOps complements template-time controls with centralized policy evaluation:
- stack/resource tags remain valid IaC baseline
- policy rules validate and enrich before provisioning paths
- deployment-time controls (such as hooks) can block noncompliant operations
Practical result:
- less manual duplication in large templates
- consistent required keys and value formats across stacks
- clearer alignment between platform standards and stack behavior
CloudFormation Template Example
AWSTemplateFormatVersion: '2010-09-09'
Description: 'Example template using TagOps CloudFormation Macro'
Transform: TagOps
Metadata:
TagOpsCustomTags:
environment: staging
team: platform
Resources:
MyBucket:
Type: AWS::S3::Bucket
Properties:
Tags:
- Key: team
Value: data-engineering
- Key: app
Value: my-appMore information and implementation examples are available in the TagOps CloudFormation integration documentation.
Closing the Out-of-Band Loophole with Event-Based Tagging
While IaC integration solves pipeline governance, platform teams must also account for manual, out-of-band changes. Resources created directly in the AWS Console (ClickOps) bypass Terraform modules and CloudFormation macros entirely.
Furthermore, IaC integrations face chronological limitations. At the time a CloudFormation macro or Terraform plan runs, the resource has not actually been
created yet. Therefore, highly dynamic context-such as the exact creation-date timestamp, or the specific IAM identity (created-by) that
initiated the deployment-is impossible to ascertain via IaC.
TagOps closes this final loophole by combining its IaC engine with Event-Based Tagging. By actively monitoring AWS CloudTrail via Amazon EventBridge, TagOps detects whenever a new resource is created in the environment-whether via IaC or manual console access. When a qualifying event occurs, TagOps instantly analyzes the CloudTrail payload, extracts the exact IAM user or role that made the API call, and dynamically tags the resource with the precise created-by identity and the exact creation date.
How TagOps Closes Each Disadvantage from Part 3
| Disadvantage from Part 3 | What goes wrong with IaC-only | How TagOps closes the gap |
|---|---|---|
| 1. Post-deploy drift | IaC fights with remediation bots over tag values. | Centralizes policy and reconciles changes back to a governed contract. |
| 2. Service-created children | Children created after the template stay partially tagged. | Event processing tags children using the same rules as parents. |
| 3. Tag Policies ≠ runtime governance | Policies define expectations but do not repair or enforce continuously. | Adds continuous event + scan enforcement on top of Tag Policies. |
| 4. Tag Policy quota pressure | Detailed logic inflates documents and hits 10k‑char limits fast. | Moves enrichment/normalization logic into a central rules engine. |
| 5. Missing-tag loopholes & SCP breakages | Hard denies block creates that will be tagged later. | Balances preventive checks with auto-correction where needed. |
| 6. Out-of-band creation | Console/API resources bypass IaC and stay ungoverned. | Event mode monitors CloudTrail and tags these resources in near real time. |
| 7. Overcorrection via strict deny | Broad denies cause failed releases and many exceptions. | Enables progressive enforcement and remediation workflows. |
TagOps Event + Scan Flows: Continuous Coverage Model
Event-Based Governance
Used for near-real-time closure:
- console-created assets
- ad-hoc API resources
- service-managed lifecycle artifacts
Scan-Based Governance
Used for residual and historical closure:
- late-discovered resources
- legacy backfill
- periodic reconciliation of partial metadata
Together, event + scan provide durable lifecycle control rather than one-time deployment control.
Reference Operating Model
- IaC baseline in Terraform/CloudFormation
- central tag contract and policy computation
- event-based auto-governance for out-of-band paths
- scan-based reconciliation loop
- KPI-driven operating cadence
KPIs to Prove Governance Maturity
- required-tag coverage %
- unknown-owner rate %
- unallocated spend trend
- mean time to remediate missing tags
- % resources governed outside pipeline path
These KPIs let teams prove that governance works in runtime reality, not only in CI logs.
Conclusion
Relying purely on Terraform, CloudFormation, and native AWS Tag Policies forces platform engineers into a cycle of managing state file drift, battling 10,000-character policy limits, and writing deployment-breaking SCPs. By integrating TagOps, organizations offload complex tagging logic to a centralized, API-driven rules engine.
Whether a resource is deployed cleanly through an IaC pipeline, or spun up manually in the middle of the night, TagOps ensures 100% tagging compliance-eliminating drift, injecting dynamic context, and restoring absolute governance to your AWS environment.
TagOps does not replace IaC. It completes IaC-based governance. Terraform and CloudFormation remain the right deployment baselines. TagOps extends policy execution across the full AWS lifecycle, so tagging governance stays accurate after deploy, outside pipelines, and during continuous infrastructure change.
Ready to unify Terraform and CloudFormation governance?
Use TagOps to apply one tagging strategy across pipelines, runtime events, and drift remediation workflows.